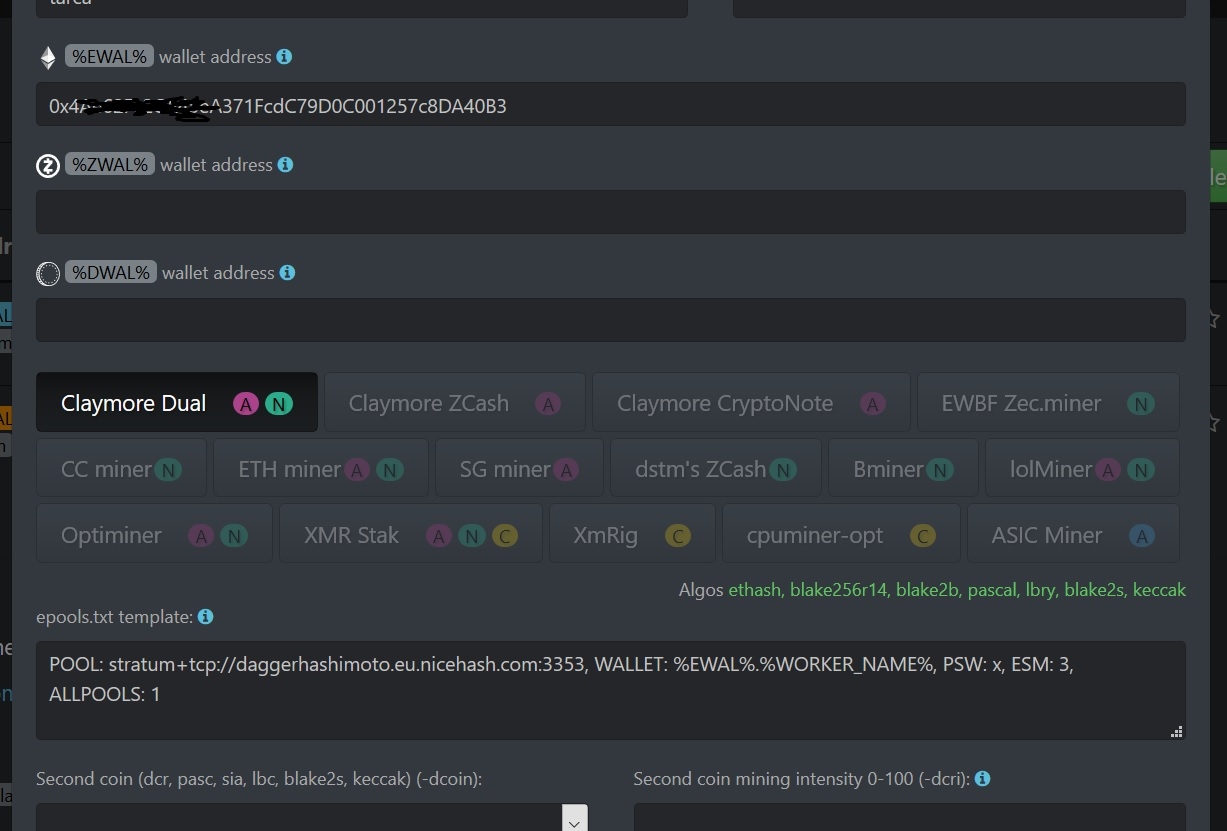
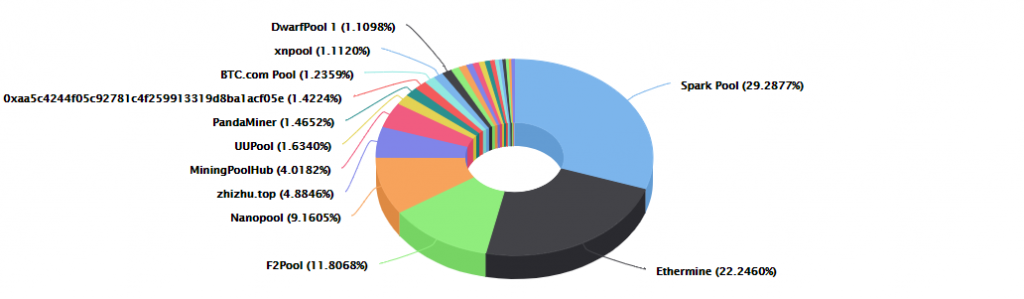
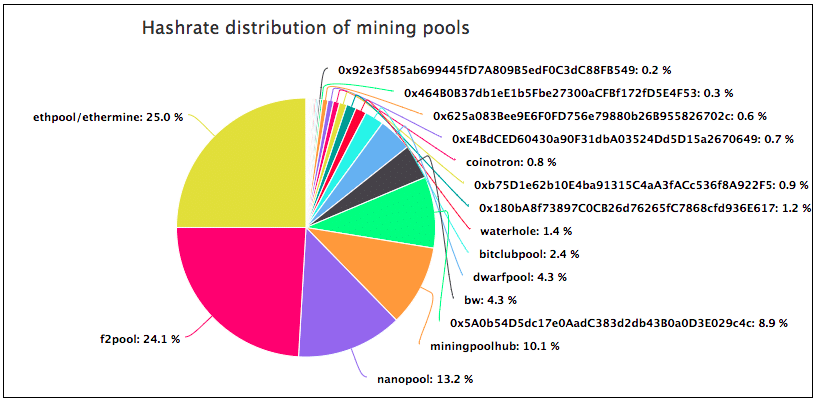
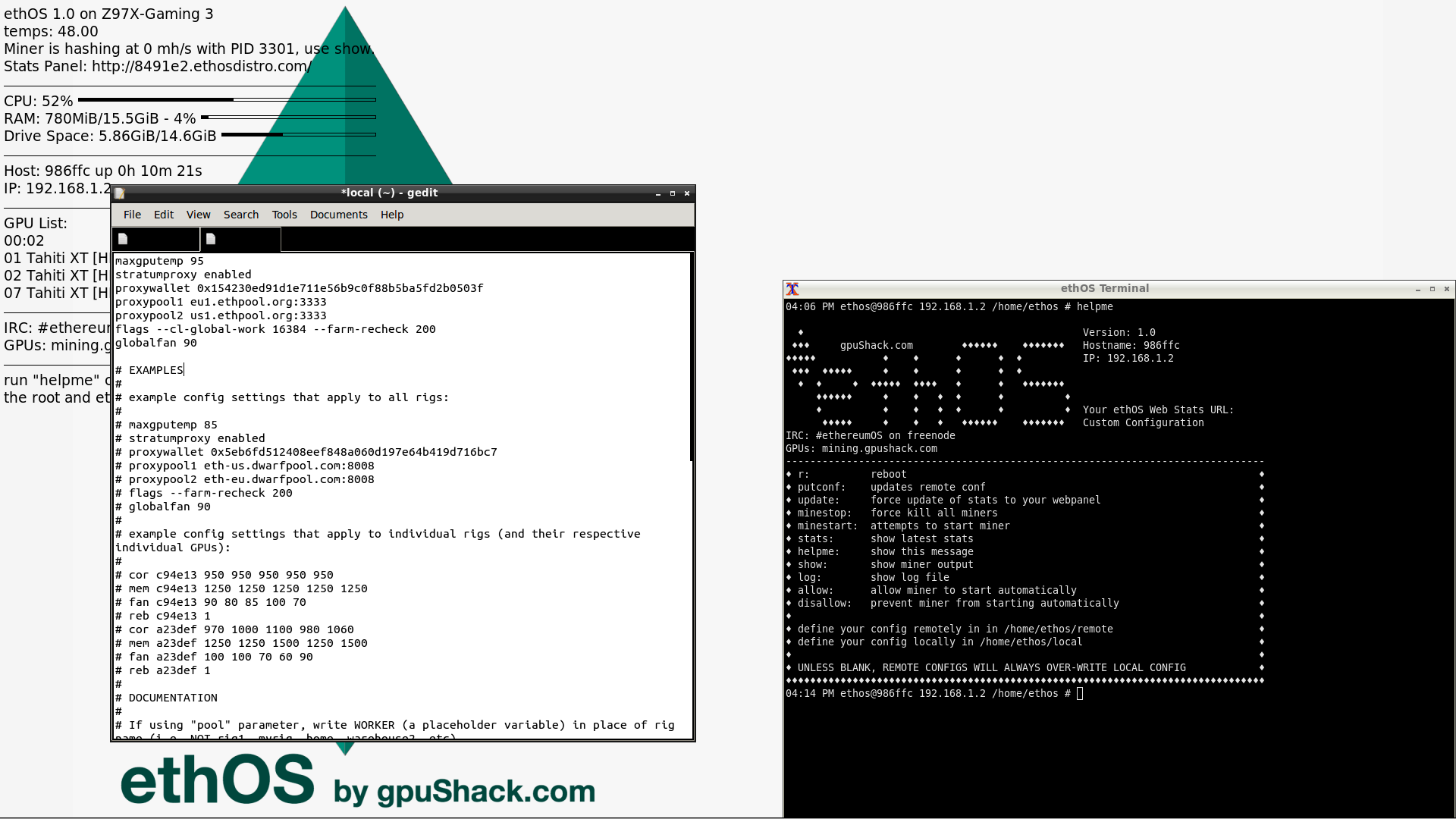
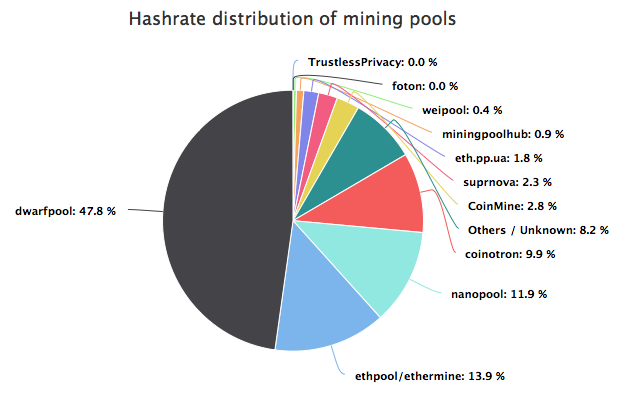
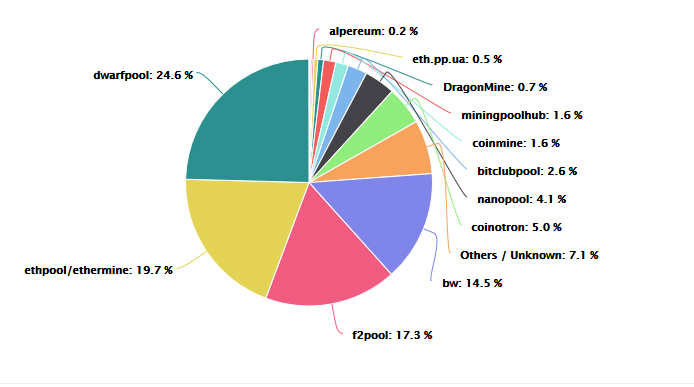
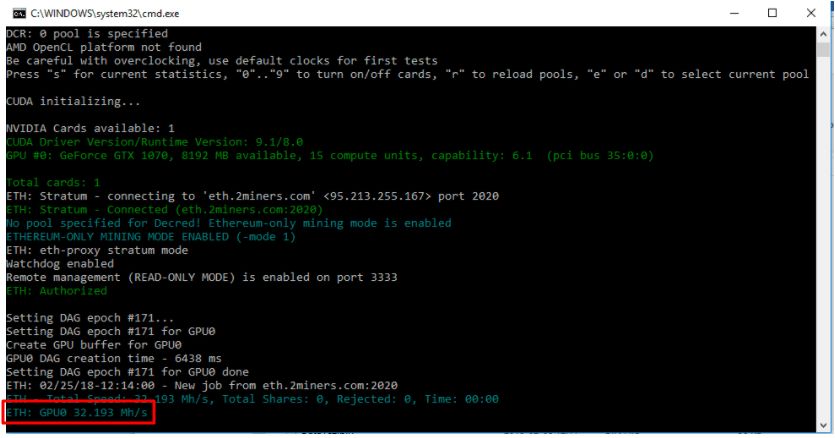
GreyNoise on Twitter: "Once the attacker identifies a server running the Claymore software they push instructions to reconfigure the device to join the "dwarfpool" mining pool and use the attacker's ETH wallet (
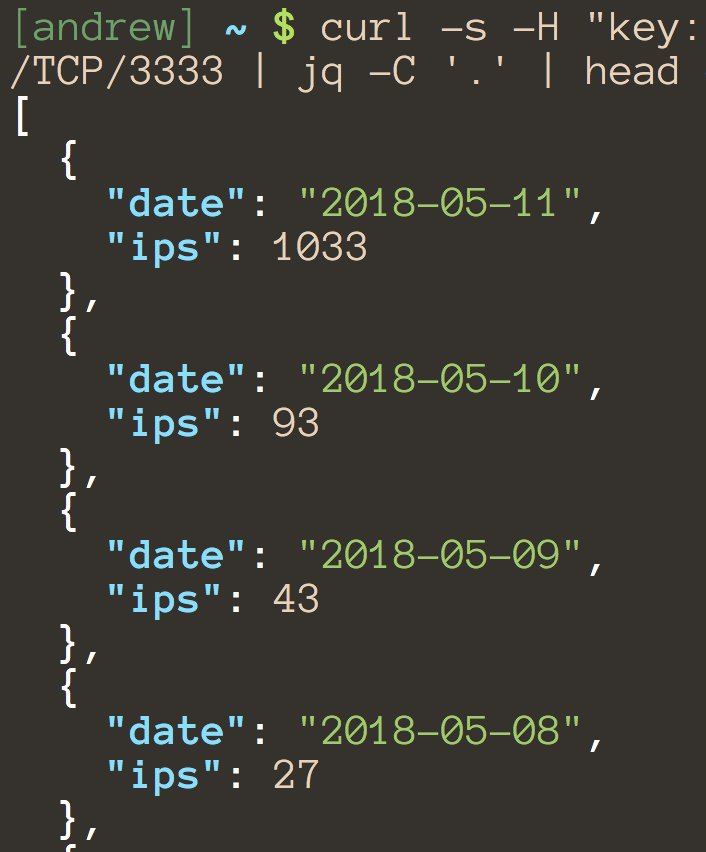
GreyNoise on Twitter: "Once the attacker identifies a server running the Claymore software they push instructions to reconfigure the device to join the "dwarfpool" mining pool and use the attacker's ETH wallet (