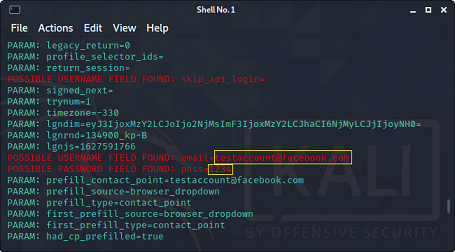
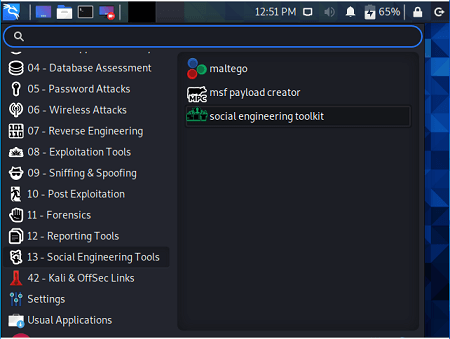
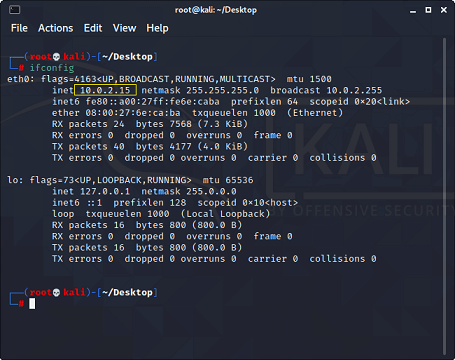
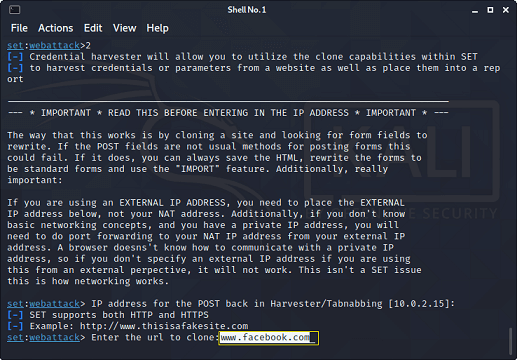
SET (Custom Import) Now, as shown in figure 12, we have to enter the IP... | Download Scientific Diagram

Amazon.com: Kali Linux: 2 books in 1: The Complete Beginner's Guide About Kali Linux For Beginners & Hacking With Kali Linux, Full of Practical Examples Of Wireless Networking & Penetration Testing: 9798637436781:

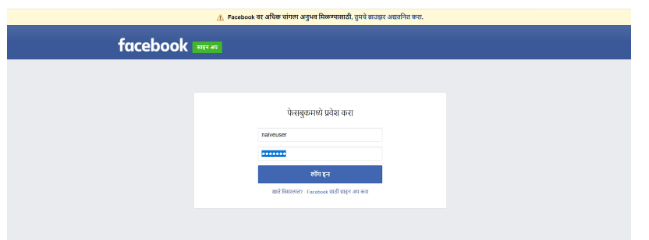
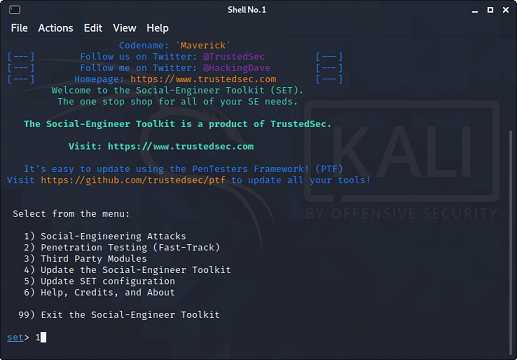
Florian Roth on Twitter: "Phishing Twitch, Netflix and Spotify users to improve over-all security. Remember ☝️ It's not that tool that is bad, it's how you use it. There are tons of